Strengthening WordPress Security with WordPress Toolkit
WordPress is the world’s most popular CMS, and for this reason, it is also the most targeted. As soon as a WordPress site goes live, automated bots begin probing for vulnerabilities. Securing WordPress sites means minimizing the attack surface.
With WordPress Toolkit for cPanel, strengthening security is easy: one click is enough to apply powerful protections.
Common WordPress vulnerabilities
- Brute force attacks: bots try to guess usernames and passwords.
- DoS/DDoS attacks: overwhelming the site’s resources, often via XML-RPC.
- Plugin and theme bugs: exploited to upload malicious code or gain privileges.
- Code injection: inserting malicious PHP, JS or SQL code.
How WordPress Toolkit improves security
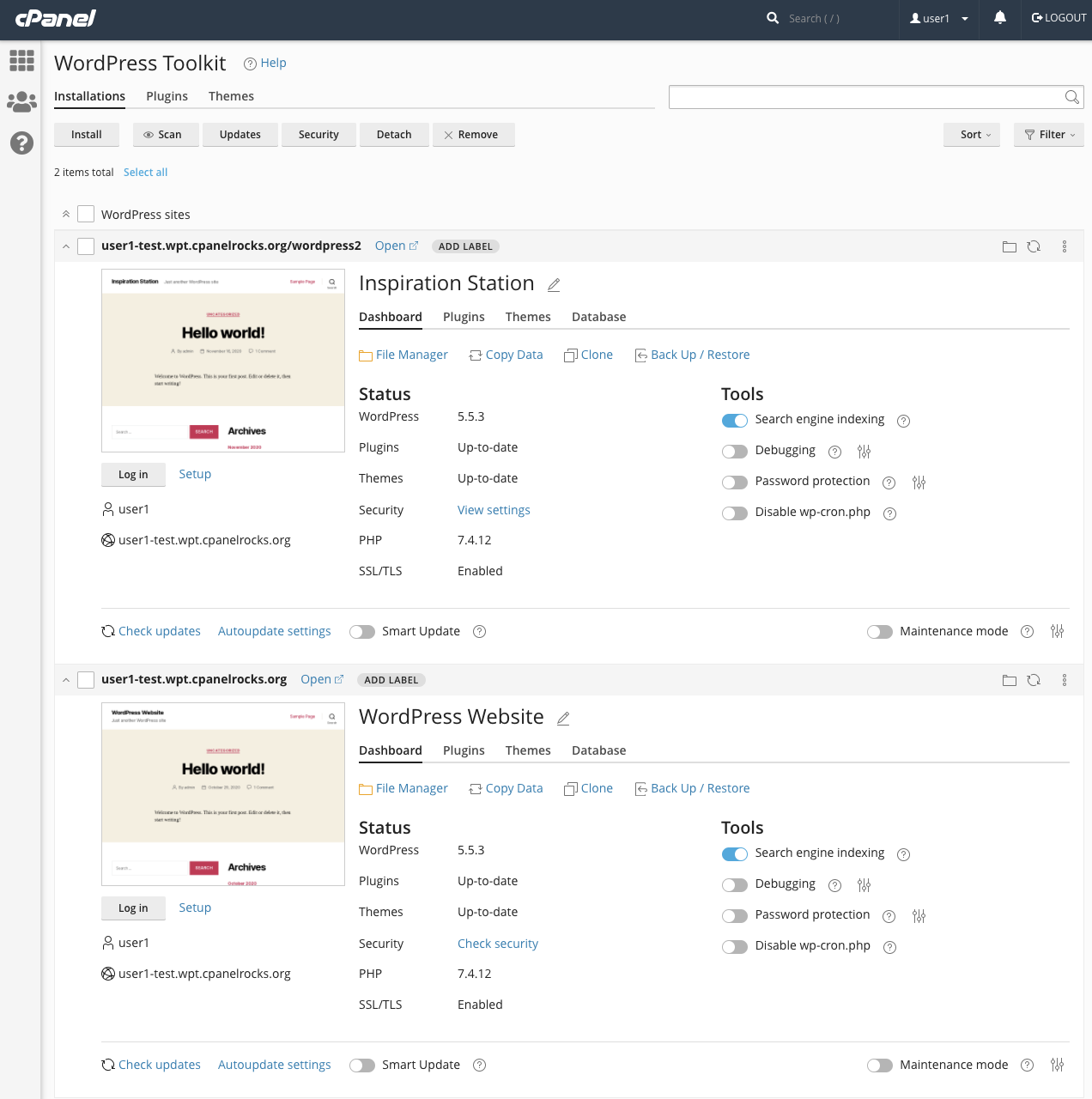
The WordPress Toolkit is a complete dashboard for WordPress management: installations, updates, backups, and security.
Key security features include:
- Automatic patching of critical vulnerabilities during installation.
- Scanning existing sites and fixing issues with one click.
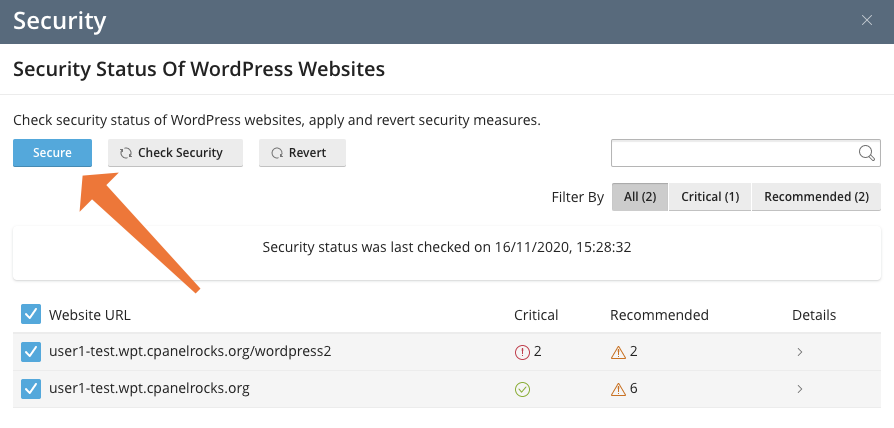
- Managing the security of multiple sites at once.
Securing a site
In the Toolkit overview, the Check Security status indicates that some measures are missing. With one click, they can be fixed.
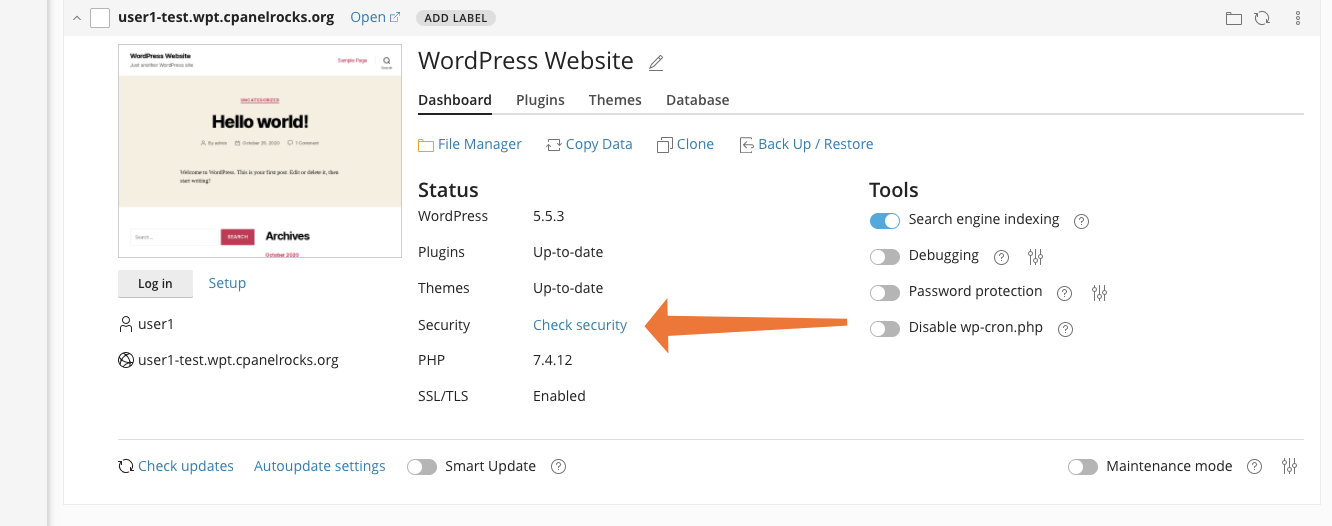
One-click protection
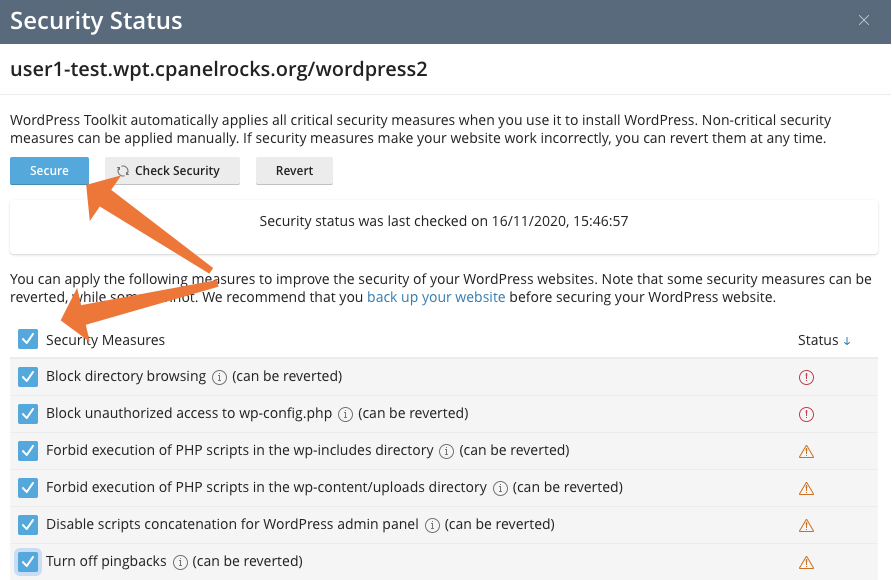
From the Security Status panel, select all measures and click Secure to apply protections automatically.
Protecting multiple sites
The Toolkit makes it possible to secure dozens or even hundreds of WordPress sites in a single operation.
Applied security measures
- Block PHP execution in
wp-includesanduploads. - Disable directory browsing and enforce secure file permissions.
- Bot protection to reduce malicious access attempts.
- Change the default admin user.
- Disable pingbacks based on XML-RPC.
- Enable hotlink protection to prevent misuse of hosted images.
Centralized updates
WordPress Toolkit lets you update Core, plugins, and themes from a single interface, preventing common exploits caused by outdated code.

